INFRASTRUCTURE SOLUTIONS
Server Infrastructure Designed for Independence, Not Dependency
From server deployment to network security, we design, build, and manage on-premises infrastructure that keeps your business running — and puts you in control. 100+ deployments since 2007 across manufacturing, IT, finance, education, and more.
50+ Companies trust Betanet-managed Infrastructure Solutions.
End-to-End On-Premises Infrastructure — Designed for Performance, Security, and Growth
Every server we deploy, every network we design, and every firewall we configure is built around one principle — your business should never depend on a single vendor, a single tool, or a single point of failure. We architect infrastructure that your team can own, operate, and scale.
Why On-Prem Deployment Fail Without The Right Partner
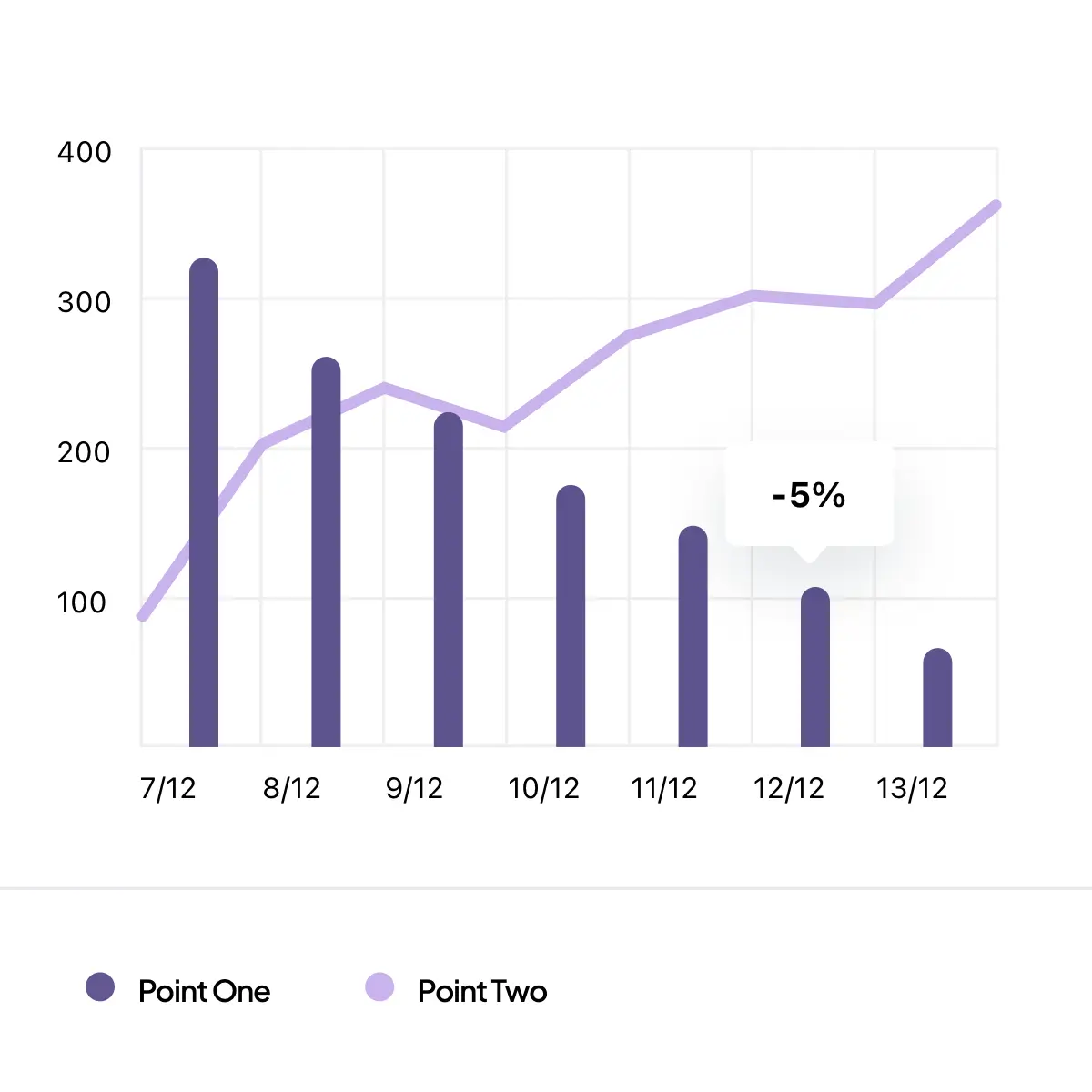
After 150+ deployments, we've seen the same patterns repeat. Companies invest in server hardware without a deployment strategy, end up with infrastructure that's overbuilt, underutilized, or impossible to manage. Here's what typically goes wrong.
Most vendors lead with a hardware quote — often ₹3-5 lakhs for a high-end server when all you need is centralized storage and Active Directory for 20 employees. Without understanding your actual workload, you end up paying for capacity you'll never use while missing configurations you actually need.
75-80% of businesses we consult operate without a domain controller — running on basic workgroup setups with no centralized user management, no group policies, and no access controls. Every employee has local admin rights, USB ports are open, and there's no audit trail for file access.
The server was set up, but nobody configured automated backups. Or backups run to the same physical disk as the data. Or the backup hasn't been tested in 18 months. When disaster strikes — hardware failure, ransomware, or an employee deleting critical files — there's nothing to recover from.
One vendor for hardware. Another for networking. A third for the firewall. A fourth for antivirus. And nobody who understands how all these layers interact. When something breaks, every vendor points to the other. Your business sits idle while they figure out whose problem it is.
On-Premises Infrastructure — Built to Last, Not Just to Launch
We don’t sell servers. We design, deploy, and manage infrastructure environments that are built around your business operations, your security requirements, and your growth trajectory. Every deployment is architected for reliability today and scalability tomorrow — with a clear path to independence.
We assess your actual workload requirements — number of users, applications, data volume, growth projections — and recommend server hardware that matches. We prefer custom Intel-based server builds that allow hardware upgrades without voiding warranties, give you better lifecycle control, and cost significantly less than branded alternatives with identical performance and durability. You're always free to purchase from any vendor — we just ensure the specifications are right.
We never do "big bang" deployments. Infrastructure goes live in phases — network first, then servers, then services, then user migration — so your business operations continue uninterrupted throughout the transition. Each phase is tested and validated before the next begins. This approach means zero or near-zero downtime, and both teams — yours and ours — can catch issues before they compound.
Every server, every configuration, every network diagram, every access credential — it belongs to you from day one. We document everything: network topology, IP assignments, PC naming conventions, access policies, backup processes, cloud configurations. When we hand over, you have a complete operational blueprint, not a black box.
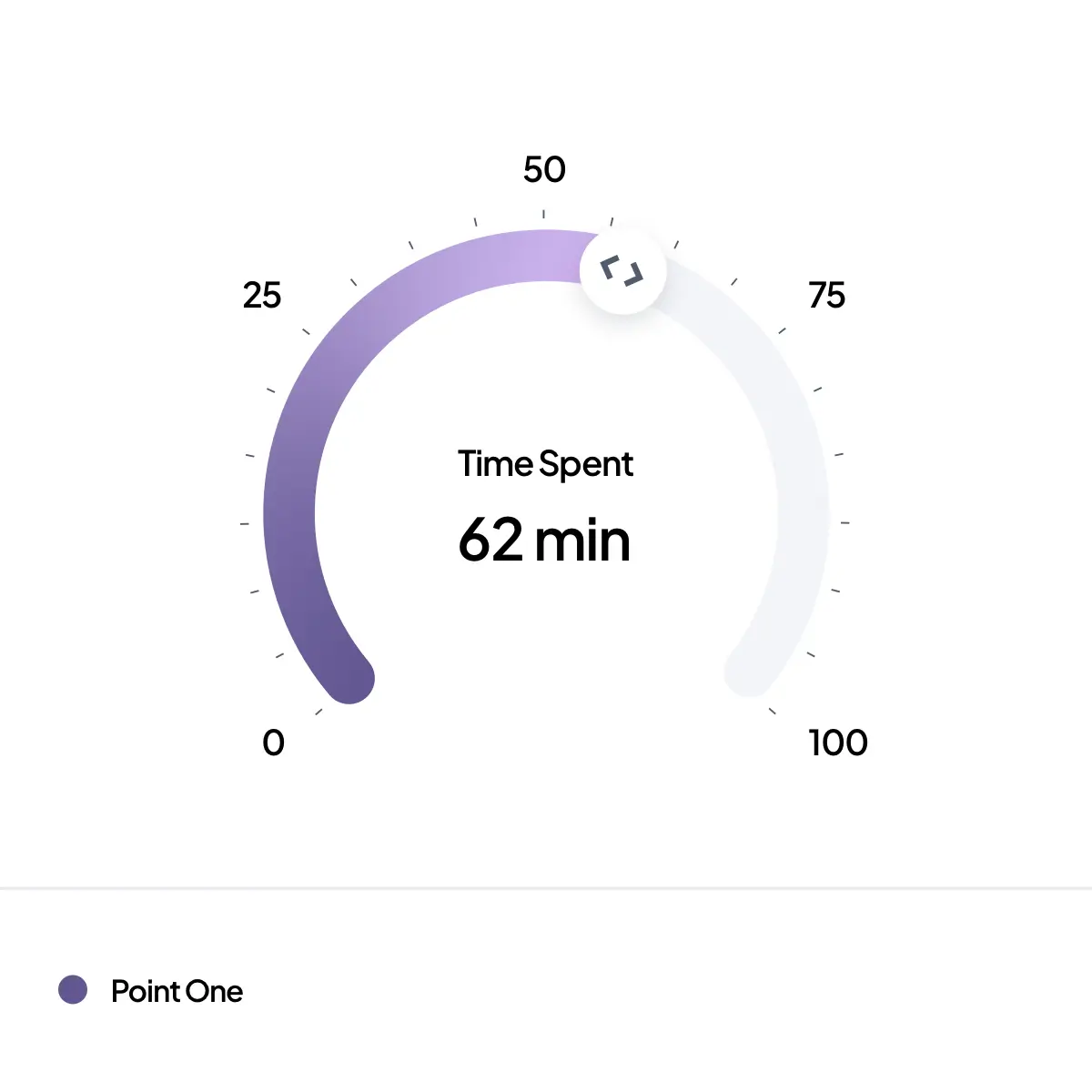
Our goal is to make you self-sufficient. After deployment, we provide 9-15 months of comprehensive support — managing firewalls, onboarding employees, handling backups, formatting PCs, configuring policies. During this period, we understand your workflows deeply enough to automate routine tasks and help you hire your own network administrator. We stay only for what genuinely requires our expertise.
Our On-Premises Deployment Methodology
Every deployment follows a proven methodology refined over 100+ implementations across 18+ years. We move from understanding your business to handing over a fully operational, documented, and secure infrastructure — with support that continues as long as you need it.
We start with a detailed discussion — not a site visit. We need to understand your business operations, employee workflows, data sensitivity, application requirements, remote access needs, growth plans, and budget constraints before we can design anything meaningful. This conversation shapes every decision that follows.
Once we understand the business requirements, we conduct a physical site survey — evaluating existing cabling, rack space, power capacity, internet connectivity, floor layout for Wi-Fi coverage, and any existing infrastructure that can be retained or upgraded. For companies with existing setups, we audit what's working and what needs replacement.
We create a complete infrastructure blueprint — network topology diagram, server specifications, IP addressing scheme, VLAN segmentation, firewall rules, backup architecture, VPN configuration, and user access policies. This document becomes your infrastructure reference manual. Nothing is deployed without your review and approval.
Based on the approved design, server hardware is procured, assembled (for custom builds), stress-tested, and pre-configured in our facility before arriving at your premises. Operating systems are installed, licensed, and updated. This pre-staging means less time on-site and fewer surprises during deployment.
Infrastructure goes live in phases to ensure zero business disruption. Typical sequence: network cabling and switching → firewall and internet → server rack and stack → Active Directory and group policies → file server and shared drives → backup configuration → VPN and remote access → endpoint deployment → monitoring tools. Each phase is tested before proceeding.
Employees are migrated to the new infrastructure in batches — joining the domain, mapping network drives, configuring email clients, setting up VPN on laptops. Your team receives hands-on training for daily operations, and we create simple documentation for common tasks like onboarding new employees, resetting passwords, and managing shared drives.
Post-deployment, we provide comprehensive support — typically 9-15 months — handling everything from firewall management to employee onboarding. During this period, we automate recurring tasks based on your workflows, monitor infrastructure health, and help you build internal IT capacity. Transition to independent management is gradual, supported, and on your timeline.
Still have questions?
Infrastructure Environments We Deploy & Manage
From Active Directory and firewalls to backup systems and remote access — every component of your on-premises infrastructure is designed, deployed, and integrated as a unified environment. Here's what a complete Betanet deployment covers.
Active Directory & Group Policy Management
Active Directory is the control center of your entire network — not just user authentication. We deploy Windows Server-based domain controllers with comprehensive group policies governing password complexity, screen lock timers, USB port access, software installation rights, and network drive mappings. Every employee gets role-based access — seeing only the files and applications their role requires. For companies running basic workgroup setups, we handle the complete migration to a domain-managed environment without disrupting daily operations. Organizational units mirror your company structure, making user management intuitive for your internal team after handover.
Firewall & Network Security
Network security starts at the perimeter and extends to every endpoint. We deploy and configure enterprise firewalls from Sophos, WatchGuard, and Fortinet, along with open-source solutions like pfSense — selecting the right platform based on your network size, compliance needs, and budget. Every deployment includes VLAN segmentation, intrusion detection and prevention, content filtering, and VPN gateway configuration. For companies needing advanced threat visibility, we deploy WAZUH as a SIEM solution — customized to log file access patterns, detect anomalies, and provide compliance-ready audit trails. We configure WAZUH to monitor what matters without capturing personal employee data. Monitoring is always transparent and declared to employees — this has been our non-negotiable policy for over 15 years.
Backup & Disaster Recovery
Description: Backups are only as good as their last successful restore. We architect multi-layer backup strategies using Robocopy for local and USB/NAS backups, and Rclone for cloud replication — eliminating expensive enterprise backup software licenses. Local backups run to dedicated NAS devices or external USB drives for air-gapped ransomware protection. Cloud backups replicate critical data to secure storage for geographic redundancy. For companies using Microsoft 365 or Google Workspace, we provide a critical additional layer — backing up OneDrive and Google Drive data to S3 storage, with read-only access provided through our secure Nextcloud portal. This protects against departing employees deleting shared files, documents, or project data from their cloud drives before exit. We currently protect 70+ employee accounts across 7-9 companies with this service. Backup health is monitored and randomly verified to ensure recoverability.
VPN & Remote Connectivity
Remote work demands more than a VPN tunnel — it demands full infrastructure access with the same security policies as the office network. We deploy Netbird-based VPN solutions that give roaming laptops complete domain integration — Active Directory authentication, group policy enforcement, mapped network drives, and shared folder access — regardless of location. Netbird is our preferred solution for 99% of deployments because it's secure, lightweight, and easy for your internal team to manage after handover. Where physical firewalls with built-in VPN are already deployed, we configure firewall-native VPN to avoid unnecessary complexity. For larger enterprises, we deploy hybrid setups with on-premises Active Directory synced to Azure AD, giving employees single sign-on across local and cloud applications.
Server Hardware & Virtualization
We don't push brands — we engineer server solutions around performance, durability, and lifecycle. For most deployments, we build custom Intel-based servers using enterprise-grade components — Samsung or Intel SSDs/NVMe, ECC memory, server-grade motherboards — delivering branded-server reliability without the restrictions. Branded servers void warranty when you modify hardware outside their approved list. Our custom builds give complete freedom to upgrade memory, add storage, or expand capacity without vendor approval or premium part pricing.
Every server is pre-configured with properly licensed Windows Server, stress-tested in our facility, and deployed ready to run. For virtualization, we deploy VirtualBox for standard use cases and Proxmox for production environments requiring snapshot-based backups and higher isolation.
Network Design & Wi-Fi Infrastructure
Network performance starts with architecture, not equipment. We design topologies based on your premises, endpoints, bandwidth requirements, and traffic patterns. Cabling is planned with proper labeling, numbering, and documentation — every port, patch, and cable run is mapped for troubleshooting and future expansion.
For switching, we deploy D-Link, Cisco, and Netgear based on network size and budget. Wi-Fi infrastructure uses Ubiquiti for larger deployments requiring seamless mesh networking across multiple floors or buildings, with simpler solutions where premises require basic coverage. Focus is always on speed and reliability — brand selection follows performance requirements, not vendor relationships.
Your Business Chooses the Tool. Not Us.
We have no brand partnerships to protect, no reseller margins to chase, and no vendor quotas to fill. When we recommend a Sophos firewall over pfSense, Ubiquiti over a basic router, or a custom server over a branded one — it's because your requirements demand it, not because our commission structure prefers it.
Enterprise Level Network Infrastrcutrue Solutions trusted by Brands.
What Makes Betanet On-Premises Infrastructure Different
What makes businesses trust a technology partner with their servers, networks, and business-critical data? Not hardware specifications — operational philosophy. These four principles have governed every on-premises deployment we have delivered since 2007, across 100+ companies, and they are the reason our clients stay for 7+ years.
We Design Before We Deploy
We do not send a hardware quote on the first meeting. Before recommending any server, firewall, or network component, we study your business operations, employee workflows, data sensitivity, and growth plans. Your infrastructure is engineered for your workload — server configuration, storage architecture, network topology, backup strategy, and security policies are designed specifically for your environment.
Right-Sized, Not Oversized
When other vendors quote ₹3-5 lakhs for a high-end server and your actual requirement is centralized storage and Active Directory for 20 employees, something is wrong. We specify hardware that matches your real workload with room to grow — custom Intel-based builds with enterprise SSDs that you can upgrade anytime without voiding warranties or paying brand premiums.
Where Security is Built-In, Not Bolted On
Where power infrastructure supports it, our server deployments run continuously for 750+ days without unplanned downtime. This reliability comes from architecture, not luck — VLAN-segmented networks, properly configured firewalls, automated backups with health verification, and group policies that prevent unauthorized access at every endpoint. Security is a design decision, not a separate line item.
Single Partner, Complete Infrastructure
Server hardware, Windows licensing, network cabling, firewall deployment, Active Directory, VPN configuration, backup architecture, cloud integration, Wi-Fi infrastructure, and employee monitoring — all managed by one team that understands how every layer connects. Your business does not need five vendors pointing fingers at each other when something breaks. One team. One call. Full accountability.
Ready to Build Infrastructure That Actually Works?
Whether you're setting up your first server or replacing infrastructure that's been failing you — the conversation starts the same way. Tell us about your business, and we'll design infrastructure around it. No hardware quotes before we understand your needs. No vendor lock-in. No dependency.
"100+ Deployments · 18+ Years · 10+ Industries · Your Infrastructure, Your Control"